Subsecond data center failover at Weller Truck Parts with HAProxy One
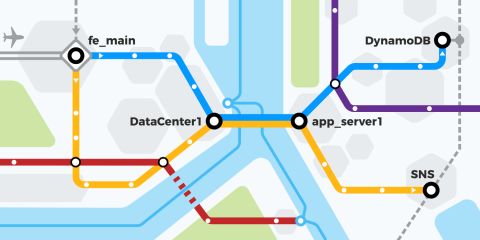
Weller Truck Parts established an active-active data center architecture with HAProxy One capable of failing over in under a second.

Weller Truck Parts established an active-active data center architecture with HAProxy One capable of failing over in under a second.

Get expert knowledge delivered directly to your inbox.
Protect your infrastructure from Drupal SQL Injection (CVE-2026-9082) using HAProxy Enterprise WAF. Learn about immediate mitigation strategies and automatic WAF protection.

The functions of application delivery, much like any traffic management and routing component, can be grouped into abstract layers called “data plane” and “control plane.”

Criteo's journey shows what HAProxy can achieve when you treat it as a programmable engine rather than a static process: a platform that adapts to demand in real time, at any scale.

HAProxy Enterprise 3.3 brings significant advancements to HAProxy Enterprise WAF and bot management capabilities. HAProxy ALOHA 18.0 delivers OWASP CRS v4 support.

Learn how HAProxy One helps PayPal Genesis manage and rapidly deploy thousands of test environments daily in a sprawling, multi-data center architecture — each with tens of thousands of containers.

KubeCon + CloudNativeCon Europe 2026 brought thousands of cloud-native practitioners to Amsterdam for four days of talks, demos, and hallway conversations about where Kubernetes is heading.

HAProxy Unified Gateway (HUG) 1.0 has officially landed — delivering unified, high-performance, cloud-native application routing. Learn how HUG's open-source design simplifies and scales Kubernetes.

Hightower has been one of the most thoughtful voices in technology for decades, with significant contributions to open source software, particularly Kubernetes.

This release marks a generational leap for the authoritative control plane that orchestrates HAProxy Enterprise’s high-performance application delivery and security.
NIS2 and DORA are now in effect. Learn how to meet EU cybersecurity and operational resilience requirements with a unified application-layer security approach.

Learn how to load balance VMware Horizon's complex UDP and TCP traffic using HAProxy's stateless stickiness. Improve remote desktop performance and reliability.

Infobip's story is a testament to how a modern, intelligent WAF can solve the complex security challenges of a global, high-performance platform.

You need a better Omnissa Horizon alternative. With HAProxy, you get superior Blast performance, eliminate hardware refresh CAPEX, and free up budget to offset rising vSphere costs.
The Ingress NGINX project is winding down. Avoid a risky 'rip and replace.' Discover the 'Shield and Shift' strategy to safely migrate to the HAProxy One platform with zero downtime.

HAProxy patch for two high-severity QUIC vulnerabilities (CVE-2026-26080, CVE-2026-26081) that allow a remote denial of service attack. Upgrade now for protection or disable the QUIC component.

HAProxy's security audit validates its zero-bug core and robust architecture. The key takeaway: security is a shared responsibility, demanding careful configuration and adherence to best practices.

By prioritizing automation and architectural freedom with HAProxy One, Dartmouth moved past the cycle of rising costs and closed ecosystems.
OpenClaw is taking over the world. However, it's brand new and its security posture is mostly unknown. Follow along as we secure OpenClaw using a battle-tested method with HAProxy.

PayPal’s Meridian is a powerful real-world use case of Universal Mesh succeeding at enterprise scale.

HAProxy Kubernetes Ingress Controller 3.2 and HAProxy Enterprise Kubernetes Ingress Controller 3.2 have arrived! These releases add powerful, user-defined annotations and a new frontend CRD.
Facing rapid growth and changing technical needs, LinkedIn made the strategic decision to redesign its traffic stack around HAProxy.

New HAProxy 3.3 and AWS-LC Performance Packages give you 50% faster TLS and linear scaling, ending a core bottleneck with other libraries.
Thanks to its design, almost all attacks that have appeared on HTTP/1 since the arrival of HTX have had no effect on HAProxy.
Protect your infrastructure from React2Shell (CVE-2025-55182) using HAProxy. Learn about immediate mitigation strategies and automatic WAF protection.

Explore the groundbreaking Intelligent WAF Engine and the key performance metrics that redefine industry standards.
Explore how HAProxy intelligently harnesses the power of modern multi-core CPUs while navigating challenging architectural complexities like NUMA.
At KubeCon, we asked a simple question at our booth: "How much is your service mesh costing you?"

Learn how Roblox's innovation journey with HAProxy provides a powerful blueprint for any organization that must deal with hyperscale growth efficiently, while maintaining robust security throughout.

HAProxy 3.3 brings downloadable packages compiled by HAProxy Technologies, numerous TLS enhancements, better observability, and many improvements to performance and flexibility.
Ingress NGINX is retiring in March 2026. Migrate now to the HAProxy Kubernetes Ingress Controller for a superior solution and a seamless path to Gateway API.

Announcing the public beta for HAProxy Unified Gateway – a free, open-source product providing Kubernetes-native application routing for Gateway API and Ingress.

HAProxy ALOHA 17.5 delivers powerful new capabilities that improve security and performance — while future-proofing HAProxy ALOHA to enable richer features and advanced functionality.

HAProxy Enterprise 3.2 brings next-generation security intelligence, extends its industry-leading performance, and expands the native routing and integration capabilities in HAProxy Enterprise.

Upgrade to the lastest version of HAProxy Kubernetes Ingress Controller (KIC) to address a vulnerability allowing privilege escalation. Learn about affected versions, remediation, and workarounds.

The latest versions of HAProxy Community and Enterprise have patches for a critical denial of service vulnerability in the mjson library.

This year at Black Hat USA, the conversation focused on model context protocol (MCP), agentic workflows, and how security fundamentals still matter.

CVE-2025-53770 and CVE-2025-53771 are currently being exploited in the wild. However, users of HAProxy Enterprise WAF are protected automatically.

A recap of the new product announcements, customer presentations, and key takeaways from HAProxyConf 2025.

HAProxy 3.2 gives you more of what matters most: exceptional performance and efficiency, best-in-class SSL/TLS, deep observability, and flexible control over your traffic.
Mitigate SAP NetWeaver CVE-2025-31324 with HAProxy. Learn how to block unauthenticated file uploads and protect your systems from severe risk.

The SSL landscape has shifted dramatically, raising questions about performance, efficiency, and costs. In this paper, we examine OpenSSL 3.x, BoringSSL, LibreSSL, WolfSSL, and AWS-LC with HAProxy.

We are experimenting with AI for prompt security in AI Gateways. Discover key lessons, performance issues, and how to optimize for practical use.

A decision-making framework breaking down the strengths, weaknesses and ideal use cases to help users choose the proper protocol for their systems.

Attendees were stunned by the scale of our presence at KubeCon London and the breadth and depth of our solutions — enabled by the HAProxy One platform.

A recently discovered security vulnerability requires attention from development teams using Next.js in production environments.

HAProxy ALOHA 17.0 introduces the new UDP Module and extends network management to the Data Plane API, a new API-based approach to network configuration.

HAProxy Enterprise 3.1 delivers a brand new ADFSPIP Module and enhancements to the HAProxy Enterprise UDP Module, CAPTCHA Module, Global Profiling Engine, and more!

HAProxy 3.1 makes significant gains in performance and usability, with better capabilities for troubleshooting. Our blog post explores all the updates.

HAProxy Kubernetes Ingress Controller 3.1 introduces expanded support for TCP CRDs, runtime improvements, and parallelization when writing maps.

HAProxy Enterprise Kubernetes Ingress Controller 3.0 is packed with powerful new features that bring greater control, performance, and observability to managing Kubernetes environments.

The latest versions of HAProxy Fusion fix multiple rsync vulnerabilities related to memory handling and file management in HAProxy Fusion’s Linux-based virtual images. We will cover these CVEs here.

AWS re:Invent 2024 has officially wrapped up, but not everything that happens in Vegas stays in Vegas. Here are some key takeaways from our five days spent with AWS and app delivery enthusiasts.

HAProxy ALOHA 16.5 is now available, bringing the new Bot Management Module, the new Network Management CLI, and more!

HAProxy 3.1 brings improvements to observability, reliability, performance, and flexibility.

Though KubeCon North America 2024 has officially come to a close, the CNCF's flagship event has left us buzzing with residual excitement. Here's what we've learned throughout those four days.

HAProxy Enterprise 3.0 extends HAProxy Enterprise’s legendary performance and flexibility and builds upon its cornerstone features.

TikTok’s web scraper, Bytespider, is reportedly aggressively sucking up content to fuel generative AI models. We also noticed this while reviewing bot management analytics. Here's what we've learned.

HAProxy Fusion 1.3 is now available! New custom dashboards, high-performance Kubernetes service discovery, and optimized workflows bolster HAProxy Fusion's observability and flexibility.

The addition of JSON and CBOR encoding in HAProxy 3.0 streamlines log management and improves interoperability between systems.

The wait is over! HAProxyConf is coming to San Francisco, California, from June 3 to 5, 2025.

Following the recent HAProxy 3.0 release, we're proud to announce that we've released HAProxy Data Plane API 3.0, which is available on our GitHub page.

HAProxy Enterprise lets you immediately drop connections and remove the client if their certificate is revoked. Here's how to strengthen security without disrupting other users and customers.

The latest versions of our products fix a vulnerability related to a possible endless loop in the HTTP/2 multiplexer when combined with zero-copy forwarding system in HAProxy, HAProxy Enterprise...

Learn how HAProxy Enterprise can help financial services uniquely identify requests as part of a greater end-to-end tracing strategy.

Securing traffic between systems is critical. Follow along as we explain how to use SPIFFE and SPIRE to automatically generate and renew identities that include mTLS certificates.

Learn why flexibility is key in modern tech stacks, how a flexible load balancer can help, and how HAProxy's unique approach gives you more freedom.

HAProxy Enterprise now supports RADIUS load balancing with the new HAProxy Enterprise UDP Module. We'll outline the challenges with implementing RADIUS load balancing and how to solve them.

AI crawlers from large language model (LLM) companies often ignore the contents of robots.txt and crawl your site. If blocking AI crawlers is your goal, HAProxy Enterprise is the answer. Here's how.

HAProxy received a Satisfaction Score of 98 in the G2 Grid® Reports for Summer 2024, and that's no accident. See how HAProxy responds to user feedback to provide a world-class customer experience.

The introduction of ChatGPT caused sharply increased interest in large language models (LLMs). These AI apps also have unique deliverability concerns. Here's how an HAProxy AI gateway can help.

Read highlights from Jakub Suchy's talk describing how HAProxy Fusion enhances both scalability and security for applications, including Kubernetes applications, on AWS.

The latest versions of our products fix a vulnerability related to HTTP/1.1 response code mishandling in products written in golang.

The latest versions of our products fix a vulnerability related to OpenSSH’s server (sshd), which is used in the public/private cloud images of HAProxy Enterprise...

HAProxy 3.0 brings many improvements to simplicity, security, reliability, flexibility, and more. We'll dive into what’s new with detailed examples. It’s a long list, so get cozy and bring a snack!

HAProxy Kubernetes Ingress Controller 3.0 is now available. In this release, we've added TCP custom resource definitions (CRDs) to improve mapping, structuring, and validation for TCP services.

HAProxy 3.0 maintains its edge over alternatives with best-in-class load balancing. Ready to upgrade? Here’s how to get started.
With HAProxy ALOHA 16 comes our next-generation WAF, new load balancing algorithms, upgraded Linux kernel to 6.1, and better isolation of admin services.

Introducing our next-generation HAProxy Enterprise WAF and HAProxy Enterprise Bot Management Module for unmatched security, performance, and reliability in a simple package.

HAProxy Fusion Control Plane enables service discovery in any Kubernetes or Consul environment without complex workarounds. Harness powerful external load balancing, multi-cluster routing, and more.

Our implementation of the HTTP/2 protocol can effectively handle the CONTINUATION Flood.

“HAProxy is an awesome load balancer,” was the common refrain on the expo floor at KubeCon Europe 2024, “but what does HAProxy do with Kubernetes?”

HAProxy Kubernetes Ingress Controller 1.11 features enhanced security with rootless containers, improved CRD management, and QUIC protocol introduction.

Different load balancer form factors don't always perform nor repackage well. Learn how HAProxy's unique software-first approach addresses common pain points when choosing the right form factor.

In this post, we will show how you can use an HAProxy Enterprise load balancer to protect against CitrixBleed by placing it in front of your NetScaler instance(s).

We have received questions regarding CVE-2023-45539 issued in November 2023. The versions of our products released on Monday, 21 August 2023 to fix...

While there are core differences between web apps and APIs, a unified security strategy is crucial. In this blog, we'll discuss why both types of security appear different yet are inherently linked.

We show you how to implement rate limiting based on the ID of the Virtual Private Cloud in Amazon Web Services using HAProxy Enterprise.

Watch our Lightning Talk at AWS re:Invent 2023 on how HAProxy Fusion and HAProxy Enterprise enable simple and scalable load balancing and security on AWS.

HAProxy 2.9 is faster, more flexible, and more observable than ever before. Ready to upgrade? Here’s how to get started.

HAProxy Fusion 1.2 brings new efficiencies, workflows, and form factors that enable you to be more productive, use more of your favorite tools, and explore powerful new use cases.

The sun has officially set on KubeCon North America 2023, but the CNCF's flagship event has left a lasting impression on us. Here's what we observed, what we talked about, and what resonated.

To avoid overspending, businesses should reevaluate their security vendors and prioritize a more cost-effective approach.

In this guide, we’ll explain why connection data matters. Next, we'll cover how the PROXY protocol works, how to use the TShark analyzer to capture and inspect packets and view the extraction results.
When it comes to key technology purchases, businesses should look for two attributes: cost efficiency and flexibility.

CVE-2023-44487 found in the HTTP/2 protocol could allow a DoS attack against web servers, reverse proxies, or other software. HAProxy products are unaffected, but we're monitoring the situation.

The G2 Fall 2023 Reports are in! HAProxy's acclaim across multiple categories, market levels, and global segments has risen. Here's what users are saying about their HAProxy use cases.

Users who upgrade to the latest versions will benefit from features that enhance the flexibility of our enterprise security options to meet even more use cases.

Modern load balancers need broad internet protocol support. We’ll outline HAProxy's product-specific protocol support, highlight core features, and share handy use cases.

HAProxy Technologies released new versions of its products to fix the vulnerability CVE-2023-40225. Learn more here.

HAProxy Technologies showcased its deep, targeted, and scalable security at Black Hat USA 2023.

In this blog post, we show how to collect HTTP header logs and store them remotely to avoid overwhelming your standard log system.

The G2 Summer 2023 Grid Reports recognize HAProxy as a leader in the Web Application Firewall (WAF) and DDoS Protection categories.

The Kubernetes Gateway API is a specification or standard managed by the SIG-NETWORK community that models service networking in Kubernetes.

Deeper mailer customization has arrived in HAProxy 2.8! Learn how Lua-based mailers improve on their C-based predecessors and support powerful new monitoring capabilities.

Improvements in acme.sh integration allows you to manage TLS certificates with Let’s Encrypt without restarting HAProxy.

Following the recent HAProxy 2.8 release, we are proud to announce that we have released HAProxy Data Plane API 2.8, available on our GitHub page.

In this article, we’ll take you on a quick tour of the new Lua event framework shipped with HAProxy 2.8—plus demonstrate how Lua helps you further customize HAProxy’s behavior.

In this blog post, we outline the steps to get started and the reasons why users are choosing to serve applications using HTTP/3 over QUIC.

We're thrilled to announce the community-driven HAProxy 2.8 release! Join us on GitHub, Slack, Discourse, and the HAProxy mailing list.

Discover more about the new, more secure, and even easier to use version 1.1 of the HAProxy Fusion Control Plane in this blog post.

In this blog post, we discuss what traffic shaping is and how you can implement it in HAProxy and HAProxy Enterprise using our bandwidth limitation filter.

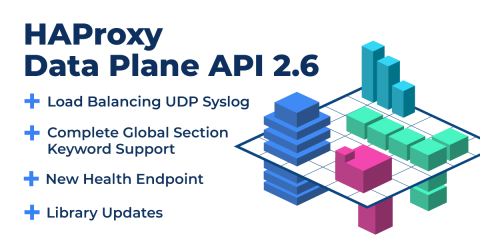
HAProxy Technologies is proud to unveil the 2.7 release of HAProxy Data Plane API. With this release, we support all HAProxy configuration keywords in the Data Plane API.

HAProxy Kubernetes Ingress Controller 1.10 is now available. HAProxy Enterprise Kubernetes Ingress Controller 1.10 is coming soon, and will incorporate these same features.In this release, we added pa

Spring marks a season of growth, and HAProxy was in full bloom in the Spring 2023 G2 reports. Our users continue to share their positive experiences .

HAProxy Enterprise 2.7 and HAProxy ALOHA 15 are now available. If you want to start the upgrade procedure straight away, go to the upgrade instructions.

KCD France 2023 was a pleasure for our team. It was great connecting with HAProxy users, especially from the Kubernetes and cloud-native community.

HAProxy Fusion Control Plane gives the power to simplify, scale, and secure HAProxy application delivery infrastructure using a centralized control plane.

HAProxy Technologies has announced that HAProxy 2.0 or newer, HAProxy Enterprise 2.0 or newer, and HAProxy ALOHA 12.5 or newer are affected by CVE-2023-25725. If you are using an affected product you

Taking the new G2 reports, user reviews, and real-world benchmark results, HAProxy stands as a market leader in application delivery and customer experience.

HAProxy 2.7 adds features such as Traffic Shaping, Stick Tables Sharding, Scalability Improvements, and Layer 7 HTTP Retry Updates.

This blog post will discuss web threats and how to protect yourself against DDoS attacks, web scraping, brute-force attacks, and vulnerability scanning.

The HAProxyConf 2022 gave us three days of workshops, keynotes, technical talks, and use cases from HAProxy core developers, community, and enterprise users.

Cookies have many usages, most notably user authentication and settings. This post will explain the best practices for how to secure your cookies.
If you are using OpenSSL version 3.0 or above with HAProxy, you should update to OpenSSL version 3.0.7.

In this blog post, you will read how containers have become one of the most efficient ways of virtually deploying applications.

In this blog post, you will learn that application acceleration is all about improving the responsiveness of a digital service.

Learn how to secure your APIs against unauthorized access. The OAuth 2 protocol uses JSON Web Tokens to convey a client’s permissions and HAProxy can verify whether a token can be trusted.
When talking about managing web applications and the services they provide, the term “API gateway” is often thrown around, but what does it mean?

In this blog, you will learn what algorithm is the best for you, both static and dynamic algorithms will help you manage incoming traffic for web applications.
In this blog post, we will explore the gold standard of high availability and the difference between a forward proxy and a reverse proxy.

Here's how to deploy the HAProxy load balancer in front of your services and then use path-based routing to direct requests to the correct backend service.

HAProxy enables mTLS, supporting client certificate authentication for both clients and backend servers. Learn how to set it up in this blog post.

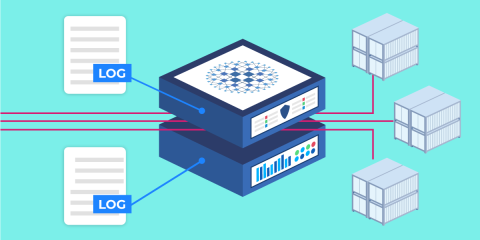
Learn how HAProxy can act as a log collection point that ingests logs from multiple applications and then forwards them to a centralized log aggregation server.

A reload clears away all of your stick table data.. The good news is that there is a way to preserve data during a reload, which we’ll cover in this blog post.

We updated the HAProxy Data Plane API to cover more HAProxy configuration keywords. In this blog, you’ll see everything we’ve added.
Do you want to talk for this year's HAProxyConf 2022? Submit your talk for this year's event which will be held on November 8 and 9 in Paris.

Learn how the HAProxy Kubernetes Ingress Controller provides a set of custom resources that includes Global, Defaults, and Backend.

In 1.8 of the HAProxy Kubernetes Ingress Controller release, we added support for full rootless mode, Prometheus metrics for the controller itself, and...

As always, the community behind HAProxy made it possible to bring the enhancements in HAProxy 2.6 release. Read on for a list of changes in HAProxy 2.6.

In this blog post, you’ll learn how the Proxy Protocol preserves a client’s IP address when that client’s connection passes through a proxy.

In this blog post, you will learn how HAProxy supports sticky sessions. You can choose to implement them either with a cookie or with the user’s IP address.

Remote Code Execution vulnerability was discovered in the Java Spring Core library. This allows attackers to execute arbitrary code on affected systems.

In this blog post, you’ll learn about several metrics that stand out as particularly useful for monitoring the health of your applications when they’re load balanced by HAProxy.

We focused on covering more HAProxy keywords, making the API a full-fledged way to configure HAProxy. In that area, version 2.5 brings a lot of improvements.

In this blog post, you'll learn how load balancing is an indispensable technique for improving a website’s performance.

Let’s consider one of HAProxy’s newest features, dynamic servers, which lets you add and remove servers from HAProxy’s load balancing list on-the-fly without ever reloading the process.

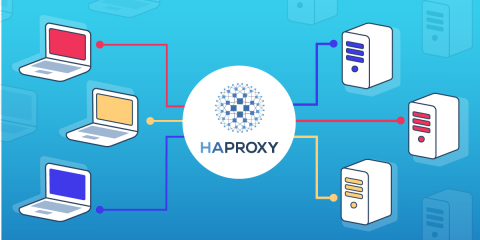
Load balancing is the distribution of network traffic between backend servers to ensure high availability and performance. Here's everything you should know.

Vulnerability which is tracked in CVE-2021-44228, dubbed Log4Shell, allows attackers to execute arbitrary code on affected systems.

We are announcing HAProxy 2.5! In this blog post, you will find a full list of improvements included in this version.

In this interview, Willy describes his views on the success of the project, and how it grew over the years.

Version 2.4 improves e2e tests, revamps how logging in the HAProxy Data Plane API works, adds support for namespace filtering in Consul Service Discovery, and much more.

In the 1.7 version of the HAProxy Kubernetes Ingress Controller, we added support for custom resource definitions that cover most of the configuration settings.

HAProxy provides three types of health checks: active health checks, passive health checks and agent health checks. In this blog, we will learn about each one.

Learned how to fine tune your HAProxy Kubernetes Ingress Controller’s configuration to leverage powerful annotations to protect your services and APIs.

If you use HAProxy 2.0 or up, you must update to the latest version. A vulnerability was found that makes it possible for an attacker to...

Learn how to safely test and validate your HAProxy config file with a single command.

In this blog post, you will learn more about HAProxy APIs and how you can manage your HAProxy configuration without editing its configuration file by hand.

In this post, you will learn how to install the open-source edition of HAProxy on Ubuntu, one of the most popular and powerful operating systems around.

If you are using HAProxy 2.0 or newer, it is important that you update to the latest version. A vulnerability was found, and here's what you should know.

Learn how to run HAProxy in a Docker container with this step-by-step guide. Covers configuration, performance considerations, security, and provides ready-to-use commands.
In this blog post, you will learn how to enable service discovery for AWS EC2 instances using HAProxy and the HAProxy Data Plane API.

Learn to configure a basic HAProxy load balancer from scratch. Our tutorial walks you through setting up frontends, backends, and simple routing rules.

In this blog post, you'll learn how to run our Kubernetes Ingress Controller externally to your Kubernetes cluster, which obviates the need for running another load balancer in front.

Do you have a topic you’d like to present? Submit your proposal! The call for papers is now open with the submission deadline set to July 5th, 2021.

In this blog, you will learn how to integrate HAProxy and Consul by using the HAProxy Data Plane API, which enables dynamic load balancer configuration changes.
In this blog post, we’ll walk through all of the steps necessary to get your HAProxy metrics displayed in InfluxDB.

HAProxy 2.4 adds features such as support for HTTP/2 WebSockets, authorization and routing of MQTT and FIX protocol messages, DNS resolution over TCP, and more.

HAProxy Data Plane API 2.3 expands its service discovery mechanisms and introduces native support for discovering AWS EC2 instances and auto-scaling groups.

Version 1.6 of the HAProxy Kubernetes Ingress Controller gives you more access to the features present in the underlying HAProxy engine. You can now...
In this blog post, we will describe how to implement autoscaling of your application pods using KEDA and the HAProxy Kubernetes Ingress Controller.

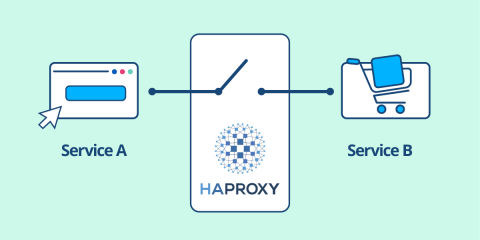
Choosing HAProxy as the proxy technology in your Consul service mesh means you’re running a high-performance solution and reducing latency between services.
First ever software load balancer exceeds 2 million RPS on a single Arm instance! We're near an era where you get the world’s fastest load balancer for free.

Having FIX available in HAProxy is great news for financial organizations. Here are the benefits of using HAProxy to route traffic to your FIX application servers.

In this blog post, we’ll see how placing your servers behind HAProxy and using it as an API gateway lets you narrow the point of entry for attackers.
![Using HAProxy as an API Gateway, Part 6 [Security]](https://cdn.haproxy.com/img/containers/partner_integrations/api-gateway-security.png/809caaf409b9cbba5f53d22b31c00307/api-gateway-security.png)
In this post, you will learn how to leverage tokens to grant some users more access than others and then charge for the service. It's called API monetization.
![Using HAProxy as an API Gateway, Part 5 [Monetization]](https://cdn.haproxy.com/img/containers/partner_integrations/api-gateway-monetization.png/f6ba7bc74399bb3dbeaec96f2813c2f7/api-gateway-monetization.png)
The HAProxy Kubernetes Ingress Controller has two sources of logs: the controller and the HAProxy load balancer. Both can be customized.
In this blog post, you'll learn about the metrics which HAProxy compiles, how to extract them with Prometheus, and visualize them with Grafana or Kibana.
![Using HAProxy as an API gateway, part 4 [metrics]](https://cdn.haproxy.com/img/containers/partner_integrations/api-gateway-4-metrics.png/bead5c0427ca39dcc7c44ed61225e630/api-gateway-4-metrics.png)
In this blog post, we will show several ways of handling multi-domain configurations, including an introduction to using HAProxy maps.

In this blog post, we show how you can use HAProxy connection limits and queues to protect your servers when load balancing heavy amounts of traffic.

The HAProxy Kubernetes Ingress Controller 1.5 release brings some exciting features that let you control the underlying configuration, and much more.

The HAProxy Data Plane API version 2.2 adds service discovery capabilities with a native Consul integration. It also introduces file handling and storage support for...

In this blog post, you'll learn how to implement a circuit breaker with HAProxy in a simple and more complex way, that allows greater customization.
In this blog post, you will learn several ways to configure HAProxy for proxying SSH, all of which rely on the ssh command's ProxyCommand field.
In this blog post, you will learn more about persistent TCP connections in an HTTP world and the various ways in which HAProxy supports it.

Log Sampling is a powerful feature introduced in HAProxy 2.0 that lets you create a representative view of your data allowing you to minimize your costs.
With HAProxy you can switch between proxying traffic at layer 4 (TCP) or layer 7 (HTTP). This blog post describes the features available to you in each mode.

Learn more about why VMware chose to partner with HAProxy Technologies and use the HAProxy as the default load balancer for its Tanzu Kubernetes clusters.

HAProxy 2.3 adds exciting features such as forwarding, prioritizing, and translating messages sent over the Syslog Protocol on both UDP and TCP, and much more.

Learn how to set up HAProxy's cache feature, which will improve how fast you can deliver messages and lessen the load placed upon your backend servers.

HTTP Strict Transport Security (HSTS) sends a user to the secure version of a site without an HTTP redirect. Learn how to enable HSTS with HAProxy.

Read on to learn how to use the HAProxy load balancer to redirect users from HTTP to HTTPS automatically in a few easy steps.

This blog post covers how to set up custom error pages in HAProxy in order to ensure consistent, branded messaging that supports any backend web stack.

Customers using HAProxy Enterprise are completely unaffected by CVE-2020-15598 because the load balancer touts a customized and hardened version of ModSecurity.

Find out how you can detect and stop fake web crawlers by using Verify Crawler add-on which comes included with the HAProxy Enterprise license.

In the blog post, you will learn how to become FIPS compliant using Red Hat Enterprise Linux 8 and HAProxy Enterprise for TLS encryption.

HAProxy Enterprise handles SAML single sign-on for your applications and integrates with identity providers like Azure Active Directory.

Learn how to use the dynamic SSL certificate storage introduced in HAProxy 2.1 and expanded in HAProxy 2.2 in order to update SSL certificates dynamically.

In this blog post, you will learn how to use HAProxy's Deny, Tarpit, Silent Drop, Reject, and Shadowban response policies to stop threats and malicious users.

Learn how to configure TLS with the HAProxy Kubernetes Ingress Controller to provide secure communication to everyone accessing your Kubernetes services.

Version 2.1 of the HAProxy Data Plane API expands support to all available request and response actions, adds Lua actions, and improves file handling.

In this blog post, you will find out more about the HAProxy Process Manager, which allows you to start external programs that are hosted under HAProxy.

HAProxy 2.2 adds exciting features such as a fully dynamic SSL certificate storage, a native response generator, security hardening, and much more.

Version 2.0 of the HAProxy Data Plane API brings exciting enhancements that unlock the power of HAProxy’s flexible configuration and its runtime capabilities.

HAProxy Enterprise will be offered in the Red Hat Marketplace, allowing OpenShift users to take advantage of its advanced features for Ingress.

Security researcher Felix Wilhelm has disclosed a critical vulnerability in HAProxy's HTTP/2 HPACK decoder in versions 1.8 and above which is now fixed.

In this blog post, we show step-by-step, how to install the HAProxy Kubernetes Ingress Controller into your Kubernetes cluster using the popular Helm charts
Learn to use the HAProxy Kubernetes Ingress Controller to host multiple tenants in a cluster and configure namespaces, access controls, and resource quotas.

This blog post covers how you can use HAProxy and the FastCGI protocol to ensure fast, secure, and observable load balancing of your PHP-FPM applications.

HAProxy Technologies is rolling out the Certified Integrations Partner Program to ensure its customers have access to integrations certified to work well.

Learn how the HAProxy Kubernetes Ingress Controller supports rolling updates and blue-green deployments for updating your Kubernetes applications.

Look back at some of the highlights from the sold-out HAProxyConf 2019, the inaugural conference for the HAProxy community.

In this blog post, you'll see examples of recent trends in the modern proxy industry and learn how HAProxy is being shaped to accommodate these changes.

HAProxy 2.1 brings visible performance gains in key areas and new features including Dynamic SSL Certificate Updates, FastCGI and a streamlined codebase.

HAProxy's origin story is one that has not been told and you may be curious about its roots and what drove it to be what it is today.

In this blog post, you’ll see how to combine HAProxy and Docker Swarm to load balance traffic across your service replicas.
Learn more about the HAProxy ALOHA PacketShield product, which provides stateful packet filtering and protects your network against DDoS.

Announcing our first-ever HAProxy user conference, HAProxyConf 2019! We’re excited about the speakers we have lined up, as well as bringing people together.

Learn more about the HAProxy Cross-Origin Resource Sharing (CORS) Lua module, which streamlines adding CORS to your APIs.

Use rate limiting in HAProxy to stop clients from making too many requests and promote fair usage of your services.

Learn how to use the HAProxy Traffic Shadowing agent to enable traffic mirroring and stream production requests to a test environment.

HAProxy 2.0 introduced layer 7 retries, which provides resilience against unreachable nodes, network latency, slow servers, and HTTP errors.

Learn how the new HAProxy Kubernetes Ingress Controller provides a high-performance ingress for your Kubernetes-hosted applications.

This blog post shows you how to use the HAProxy Data Plane API to manage your load balancer configuration dynamically using HTTP commands.

This blog post shows how to quickly and easily enable SSL/TLS encryption for your applications by using high-performance SSL termination in HAProxy.

HAProxy Technologies is excited to announce the release of HAProxy 2.0, bringing features critical for cloud-native and containerized environments.
Learn how to use DNS service discovery in HAProxy to detect server changes and automatically apply them to your configuration.

HAProxy integrates with AWS X-Ray to give you the best observability across your Amazon Web Services (AWS) resources, including your load balancer.
This blog post demonstrates how you can use custom Lua code to extend HAProxy for creating your own fetches, converters, actions, services, and tasks.

Learn to monitor, troubleshoot, and manage your load balancer effectively with our deep dive into the HAProxy status page.

In this blog post, learn to use HAProxy, Keepalived, Terraform, and Ansible to set up highly-available load balancing in AWS.
In this blog, we’ll explain how to set up the metrics endpoint, how to configure Prometheus to scrape it and offer guidance on graphing and alerting the data.
Learn how to use The HAProxy Stream Processing Offload Engine (SPOE) filter to extend HAProxy in any language without modifying its core codebase.

This blog post shows how to use HAProxy IP Masking in order to protect the privacy of your users, helping you to stay compliant with laws like the GDPR.

In the blog post, you'll learn various ways to health check your servers so that your APIs maintain a high level of reliability. This includes...
![Using HAProxy as an API gateway, part 3 [health checks]](https://cdn.haproxy.com/img/containers/partner_integrations/image2-2-%281%29.png/5ef4ef148b968f89804293c3d44312e7/image2-2-%281%29.png)
The Power of Two Random Choices load-balancing algorithm made us curious. See how it stacks up against other modern-day algorithms available in HAProxy.

Master HAProxy logging with our step-by-step guide. Learn to configure logging, understand TCP & HTTP log formats, and parse log files for critical infrastructure insights.

In the blog post, you'll learn more about using HAProxy as an API gateway, leveraging it to secure your API endpoints using OAuth 2.
![Using HAProxy as an API Gateway, Part 2 [Authentication]](https://cdn.haproxy.com/img/containers/partner_integrations/image2-e1548174430466.png/3942e9fa498bb46e325ba72db6f9bd84/image2-e1548174430466.png)
Learn how to set up an example project that uses gRPC and Protocol Buffers to stream messages between a client and a server with HAProxy in between.

Announcing the release of HAProxy 1.9, which brings end-to-end HTTP/2, buffer and connection management improvements, native HTTP representation, and more.

In a service mesh, requests are passed to proxies that relay messages from one service to another. See how HAProxy can be used in the Consul service mesh.

HAProxy has best-in-class bot protection capabilities for detecting and defending against many types of unwanted bot traffic. Read on to learn how.

HAProxy's high-performance security capabilities are utilized as a key line of defense by many of the world's top enterprises. Application layer DDoS attacks are aimed at overwhelming an application w

This guide explains the 4 core sections and key directives such as setting the haproxy default timeout, timeout client, and timeout server.

In this post, you’ll learn how to create an HAProxy map file, store it on your system, reference it in your HAProxy configuration, and update it in real time.

In this blog post, we'll demonstrate how to place HAProxy at the edge of your AWS infrastructure without involving Elastic Load Balancing (ELB).

An API gateway routes client requests intelligently and handles functions such as load balancing, security, and rate limiting.
![Using HAProxy as an API gateway, part 1 [introduction]](https://cdn.haproxy.com/img/containers/partner_integrations/2022/api-gateway-pt1/avalanche-area-1080x540.png/2b915c11c726470bf6e314e194c3a7ed/avalanche-area-1080x540.png)
Learn more about HAProxy's fast, in-memory storage called stick tables that let you track user activities, including malicious ones, across requests.

A practical guide to HAProxy ACLs. Learn the syntax and follow step-by-step examples to block traffic, redirect users, choose backends, and enhance security.

HAProxy offers a patch set for enabling seamless reloads of HAProxy without dropping packets in the process. In this blog post, we show you how to enable this.

HAProxy Technologies is proud to announce the availability of an integrated Let’s Encrypt ACMEv2 Lua client for HAProxy and HAProxy Enterprise (HAPEE).

We are very excited to announce the release of HAProxy Enterprise 1.8r1, which is built on top of the monumental stable release of HAProxy 1.8.

In this blog post, we will show you a zero-touch method for integrating HAProxy with Consul by using DNS for service discovery available in HAProxy 1.8.

In this blog post, we'll demonstrate how to use HAProxy in combination with Amazon Elastic Load Balancing (ELB) and Amazon Application Load Balancer (ALB).

This blog post will provide an introduction to multithreading functionality in HAProxy, its configuration, and basic troubleshooting procedures.

LLC. is pleased to announce that HAProxy Enterprise Edition, the commercial version of its popular load balancer, is now available on AWS Marketplace.

In this blog post, we'll take you on a tour of the HAProxy Runtime API and its capability to dynamically configure ACLs, stick tables and TLS ticket keys.

Transport Layer Security (TLS) is a cryptographic protocol that enables secure communications over a computer network.

The monumental stable release of HAProxy 1.8 is here! The HAProxy 1.8 release candidate 1 (RC1) has been published by the R&D team here at HAProxy Technologies.

Microservices architectures require the ability to make frequent app delivery changes in an automated and reliable way. The HAProxy Runtime API enables this.

What users often call a “seamless” or “hitless” reload is a configuration update or a service upgrade performed with no impact on user experience.

Why use the Proxy protocol? Well, when you lose client information like IP address when relaying connections through proxies, this tends to prevent you from...

We're willing to offer a couple of load balancers for free to any student or intern who can describe a project they're working on that involves load balancing.

This is the ALOHA Pocket. Probably the smallest load balancer you have ever seen from any vendor.

This blog contains information and provides a technical guide for getting started with the ELK stack, configuring HAProxy, parsing the data and troubleshooting.

In a Slow POST attack, an attacker begins by sending a legitimate HTTP POST header to a Web server, exactly as they would under normal circumstances.

In this blog post, we will answer this question: how to follow up on a container IP change when restarting a container?

13th of October 2015, Willy Terrau announced the release of HAProxy 1.6.0, after 16 months of development. A total of 1156 commits from 59 people were committed.

In this blog post, we will give a quick step-by-step guide on how to serve ECC and RSA certificates on the same IP with HAProxy.

In this blog post, we will show how to use HAProxy's hash based load balancing algorithm for static content delivery with Varnish.

Remote Desktop Services is a technology from Microsoft that allows users to remotely access a session-based desktop, virtual machine-based desktop, or...

Health checking is one of the most important features of a load balancer. Here we show how to match multiple conditions for HTTP health checking in HAProxy.

This blog post explains how to use HAProxy to simply prevent using SSLv3 or to prevent those users to reach your applications and print them a message.

Today’s article will explain how to use HAProxy to protect your application from Bash shellshock vulnerability if you’re in a case where you have to be protected.

In this blog post, we demonstrate how to enable binary health checks with HAProxy 1.5 by using a PHP-fpm/FastCGI probe example.

The HTTP 408 status code is an error returned by the server when it doesn't receive a timely request from the client.

Some customers ask us to migrate the Apache mod_proxy configuration into HAProxy. This article explains how to translate ProxyPass-related rules.

In this blog post, we will demonstrate how to perform asymmetric routing and multiple default gateways on Linux with HAProxy.

You don’t want your clients to send their cookies (understand their identity) clearly through the Internet. This is today’s article's purpose.

In this blog post, we will show the different ways in which you can use the HAProxy load balancer to emulate an active/passive clustering mode.

In this blog post, we demonstrate how to build a simple Redis infrastructure thanks to the HAProxy advanced send/expect health checks feature.

HAProxy allows to redirect traffic based on events and internal status. In this blog post we show how to use HAProxy for failover and worst-case management.

Basically, HAProxy uses the NPN (and later the ALPN) TLS extension to figure out whether the client can browse the website using SPDY.

Here comes the transparent proxy mode: HAProxy can be configured to spoof the client IP address when establishing the TCP connection to the server.

In this blog post, we show how you can enable inserting client certificate information in HTTP headers and reporting them in the log line with HAProxy.

In this blog post, we provide an HAProxy configuration that can help you detect the Apache Cdorked Backdoor attack in your systems and protect them against it.

A brute force attack in WordPress consists of massively sending requests to a URL with different parameters each time. Here's how to prevent it using HAProxy...

In this blog post, we show two ways of performing source IP affinity with HAProxy: through the hash load balancing algorithm and using HAProxy Stick Tables.

In this blog post, we describe how you configure HAProxy to log URLs exactly the way they were sent by the client by using syslog-ng's flexible configuration.

When setup by the application server, the HAProxy load balancer can be used to update cookies on-the-fly. In this blog post, we explain how.

Performing SSL at the Load-Balancer Layer is called SSL offloading because you offload this process from your application servers. Here's what you should know.

The BEAST attack on SSL isn’t new, but we have not yet published an article to explain how to mitigate it with ALOHA or HAProxy.

In this blog post, we show how to perform load balancing with HAProxy on Microsoft Exchange 2013 Services hosted on single and multiple host names.

In this blog post, we show how to use HAProxy with MySQL at high request rates, and how to prevent the common TCP source port exhaustion error.

In this blog post, we will provide information on how to enable Exchange Outlook Web Access (OWA) Cross-Site Request Forgery (CSRF) protection with HAProxy.

HTTP protocol is connection-less and only the client can request information from a server. In any case, a server can contact a client. Furthermore...

This guide shows you how to use the 'log-format' directive, variables, and captured headers to create the perfect log for your needs.

Compression is used for reducing object size in order to reduce delivery delay for objects over the HTTP protocol. We show how to enable this in HAProxy.

In this blog post, we will demonstrate how to create a highly performant WAF platform using Naxsi and the HAProxy load balancer.

The below information is deprecated as HAProxy Enterprise now offers a fully functional native WAF module which supports whitelist-based rulesets, and more.

The main purpose of using client-side certificates is to increase the level of authentication. Since HAProxy is often in front of web platform, it is the right place to do this authentication.

In this blog, we share how to build a high-available RTMP platform for delivering video content with HAProxy and crtmpserver.

In this blog post, we will show how to use HAProxy's layer 7 features to improve eCommerce website performance and provide the best end-user experience.

HAProxy is a high-performance reverse proxy and load balancer commonly used on web platforms and even as a replacement for hardware load balancers like F5 appliances.

HAProxy can support SSL offloading. Today, I’ll focus on how to install and configure HAProxy to offload SSL processing from your servers.

In this blog post, we'll explain how to use both HAProxy and Varnish on a web application hosted on a single domain name.

Despite being “competitors”, each of them has its own very well performing: HAProxy is a Reverse-proxy Load-Balancer and Varnish is a Reverse-proxy cache.

In this blog post, we will provide a configuration that you can use to protect your applications against HTTP request flood attacks.

Geolocation is the process of linking a third party to a geographical location. In easier words: know the country of a client's IP address. On the Internet, such a base is called GeoIP.

In this blog post, we will explain how to configure the HAProxy load balancer to build an efficient SMTP relay infrastructure with Postfix.

In this blog post, we aim to demonstrate how to preserve source IP addresses when using the reverse-proxy mode in HAProxy.

In this blog post, we summarize the findings of a hypervisors virtual network performance comparison from a virtualized load balancer point of view.

In this blog post, we show how to enable enhanced SSL load balancing with the Server Name Indication (SNI) TLS Extension in HAProxy and HAProxy ALOHA.

This blog post shows why and how to use a load balancer, the differences between Affinity, Persistence, and Sticky Sessions, and how to enable them in HAProxy.

Microsoft Terminal Services or remoteapps both use the RDP protocol. One issue when using RDP is being able to stick a user to a server.

This blog post will show you how to use HAProxy ALOHA as a reverse proxy for accessing multiple websites or apps behind a single public IP address.

In this blog post, we explain how one can improve SSL/TLS performance by adding some functionality to SSL open-source software with HAProxy.

In this blog post, we explain what the Layer 4 Load Balancing Direct Server Return (DSR) Mode is, its pros and cons and when and how to use it.

In this blog post, we explain what the Layer 4 load balancing tunnel mode is, how it works, when to use it, as well as its pros and cons.

In this blog post, we explain what the Layer 4 Load Balancing NAT Mode is, its pros and cons and when to use this type of architecture.

In this blog post we will demonstrate how you can send users to the same server for imap and smtp by using HAProxy ALOHA.

Your application uses both HTTP and HTTPS, depending on the pages. SSL encryption is achieved by your backend server directly. Here's how.

Slowloris is a script which opens TCP connections and sends HTTP headers very slowly to force web servers to keep connections opened. The purpose is to...

HAProxy ALOHA allows you to maintain HTTPS sessions based on SSL connection ID. In this blog post, we show you how to configure HAProxy ALOHA for this.

In this blog post we demonstrate how to protect any application or web server against unexpected high load using HAProxy ALOHA.

Build a scalable architecture for a news website using these components: A load balancer with content switching capability, cache server and application server.

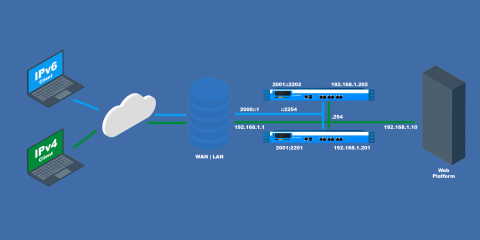
In this blog post, we show how to configure HAProxy Aloha to use it as an IPv6 to IPv4 gateway without modifying anything on your current platform.
Layer 4 is related to the transport layer of the OSI model, and layer 7 is related to the application level. A layer 7 load balancer makes routing decisions based on...
