Kubernetes Ingress Controller
High-performance ingress for Kubernetes apps
Route external traffic into your Kubernetes clusters using the Ingress API. Secure, efficient, highly scalable, and perfectly integrated with Kubernetes tooling and workflows.
Master your Kubernetes app traffic
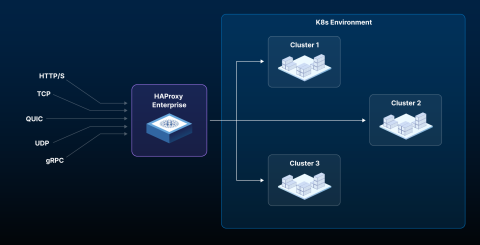
HAProxy Enterprise Kubernetes Ingress Controller acts as a proxy inside the cluster and maps incoming requests to multiple services. Greatly reduce the complexity of connecting external clients to your containerized applications.
Handle tens of thousands of requests per second on one instance — with the highest average throughput, lowest latency, and lowest CPU usage. Support your most demanding applications without breaking the bank.
Deploy inside or outside of Kubernetes according to your needs. Broad protocol support and multiple load-balancing algorithms support your K8s apps. Kubernetes API and CRD integration help you manage K8s how you want.
Implement transparent and industry-standard security for your Kubernetes applications with our embedded WAF, rootless design, and resilient architecture.
Verbose logging and statistics give insight into the health of your pods, current request rates, response times, and errors.

One solution for everything Kubernetes
Our comprehensive Kubernetes networking solution for on-premises and cloud deployments also includes intelligent external load balancing, multi-cluster routing, and blue-green deployments, enabled by HAProxy Enterprise and HAProxy Fusion.
Key HAProxy Enterprise Kubernetes Ingress Controller capabilities
Learn how to simplify your Kubernetes infrastructure, supercharge performance, and seamlessly secure your clusters.
Seamless integrations with essential tech
What are users saying about HAProxy Enterprise Kubernetes Ingress Controller?
"HAProxy Enterprise allowed us to combine our software load balancer and web application firewall layers, which simplified the architecture, improved performance, and reduced costs.
We deployed the HAProxy Enterprise Kubernetes Ingress Controller to further simplify our application delivery while also staying compliant with federal regulations."
"I use HAProxy as a round robin point of ingress to k8s clusters. Works reliably and has never not worked."
Featured Resources
Learn tips, tricks, and best practices for getting the most out of HAProxy Enterprise Kubernetes Ingress Controller — and stay up to date with new product developments.
Announcing HAProxy Kubernetes Ingress Controller 3.2
HAProxy Kubernetes Ingress Controller 3.2 and HAProxy Enterprise Kubernetes Ingress Controller 3.2 have arrived! These releases add powerful, user-defined annotations and a new frontend CRD.
Read more
Using CRDs to improve quality of life in Kubernetes
In this webinar, you’ll learn how custom resources simplify ingress controller management and allow you to interact with the controller using familiar tools.
Watch now