Announcing HAProxy 3.4
HAProxy 3.4 brings important improvements to flexibility, performance, security, reliability, and more.

Nick creates technical content for HAProxy Technologies ranging from documentation and blog posts to Wikipedia articles, GitHub READMEs and Stack Overflow answers. With a background in web development and DevOps, he has fun digging into product features and discovering the optimal path for a new blog tutorial.
Twitter LinkedIn GitHubHAProxy 3.4 brings important improvements to flexibility, performance, security, reliability, and more.
HAProxy 3.1 makes significant gains in performance and usability, with better capabilities for troubleshooting. Our blog post explores all the updates.

HAProxy 3.0 brings many improvements to simplicity, security, reliability, flexibility, and more. We'll dive into what’s new with detailed examples. It’s a long list, so get cozy and bring a snack!

HAProxy 3.0 maintains its edge over alternatives with best-in-class load balancing. Ready to upgrade? Here’s how to get started.
HAProxy 2.9 is faster, more flexible, and more observable than ever before. Ready to upgrade? Here’s how to get started.

CVE-2023-44487 found in the HTTP/2 protocol could allow a DoS attack against web servers, reverse proxies, or other software. HAProxy products are unaffected, but we're monitoring the situation.

HAProxy Technologies released new versions of its products to fix the vulnerability CVE-2023-40225. Learn more here.

We're thrilled to announce the community-driven HAProxy 2.8 release! Join us on GitHub, Slack, Discourse, and the HAProxy mailing list.

Discover more about the new, more secure, and even easier to use version 1.1 of the HAProxy Fusion Control Plane in this blog post.

HAProxy 2.7 adds features such as Traffic Shaping, Stick Tables Sharding, Scalability Improvements, and Layer 7 HTTP Retry Updates.

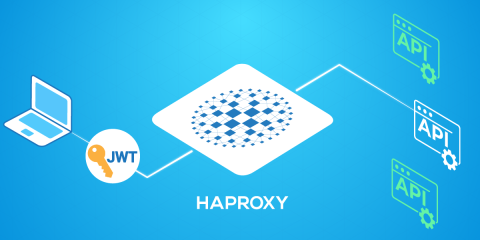
Learn how to secure your APIs against unauthorized access. The OAuth 2 protocol uses JSON Web Tokens to convey a client’s permissions and HAProxy can verify whether a token can be trusted.
Here's how to deploy the HAProxy load balancer in front of your services and then use path-based routing to direct requests to the correct backend service.

HAProxy enables mTLS, supporting client certificate authentication for both clients and backend servers. Learn how to set it up in this blog post.

Learn how HAProxy can act as a log collection point that ingests logs from multiple applications and then forwards them to a centralized log aggregation server.

A reload clears away all of your stick table data.. The good news is that there is a way to preserve data during a reload, which we’ll cover in this blog post.

Learn how the HAProxy Kubernetes Ingress Controller provides a set of custom resources that includes Global, Defaults, and Backend.

As always, the community behind HAProxy made it possible to bring the enhancements in HAProxy 2.6 release. Read on for a list of changes in HAProxy 2.6.

In this blog post, you will learn how HAProxy supports sticky sessions. You can choose to implement them either with a cookie or with the user’s IP address.

In this blog post, you’ll learn about several metrics that stand out as particularly useful for monitoring the health of your applications when they’re load balanced by HAProxy.

In this blog post, you'll learn how load balancing is an indispensable technique for improving a website’s performance.

Let’s consider one of HAProxy’s newest features, dynamic servers, which lets you add and remove servers from HAProxy’s load balancing list on-the-fly without ever reloading the process.

Load balancing is the distribution of network traffic between backend servers to ensure high availability and performance. Here's everything you should know.

HAProxy provides three types of health checks: active health checks, passive health checks and agent health checks. In this blog, we will learn about each one.

If you use HAProxy 2.0 or up, you must update to the latest version. A vulnerability was found that makes it possible for an attacker to...

In this blog post, you will learn more about HAProxy APIs and how you can manage your HAProxy configuration without editing its configuration file by hand.

Learn how to run HAProxy in a Docker container with this step-by-step guide. Covers configuration, performance considerations, security, and provides ready-to-use commands.
Learn to configure a basic HAProxy load balancer from scratch. Our tutorial walks you through setting up frontends, backends, and simple routing rules.

In this blog post, you'll learn how to run our Kubernetes Ingress Controller externally to your Kubernetes cluster, which obviates the need for running another load balancer in front.

In this blog, you will learn how to integrate HAProxy and Consul by using the HAProxy Data Plane API, which enables dynamic load balancer configuration changes.
In this blog post, we will describe how to implement autoscaling of your application pods using KEDA and the HAProxy Kubernetes Ingress Controller.

Choosing HAProxy as the proxy technology in your Consul service mesh means you’re running a high-performance solution and reducing latency between services.
In this blog post, we’ll see how placing your servers behind HAProxy and using it as an API gateway lets you narrow the point of entry for attackers.
![Using HAProxy as an API Gateway, Part 6 [Security]](https://cdn.haproxy.com/img/containers/partner_integrations/api-gateway-security.png/809caaf409b9cbba5f53d22b31c00307/api-gateway-security.png)
In this post, you will learn how to leverage tokens to grant some users more access than others and then charge for the service. It's called API monetization.
![Using HAProxy as an API Gateway, Part 5 [Monetization]](https://cdn.haproxy.com/img/containers/partner_integrations/api-gateway-monetization.png/f6ba7bc74399bb3dbeaec96f2813c2f7/api-gateway-monetization.png)
In this blog post, you'll learn about the metrics which HAProxy compiles, how to extract them with Prometheus, and visualize them with Grafana or Kibana.
![Using HAProxy as an API gateway, part 4 [metrics]](https://cdn.haproxy.com/img/containers/partner_integrations/api-gateway-4-metrics.png/bead5c0427ca39dcc7c44ed61225e630/api-gateway-4-metrics.png)
In this blog post, we show how you can use HAProxy connection limits and queues to protect your servers when load balancing heavy amounts of traffic.

In this blog post, you'll learn how to implement a circuit breaker with HAProxy in a simple and more complex way, that allows greater customization.
With HAProxy you can switch between proxying traffic at layer 4 (TCP) or layer 7 (HTTP). This blog post describes the features available to you in each mode.

Learn how to set up HAProxy's cache feature, which will improve how fast you can deliver messages and lessen the load placed upon your backend servers.

HTTP Strict Transport Security (HSTS) sends a user to the secure version of a site without an HTTP redirect. Learn how to enable HSTS with HAProxy.

Read on to learn how to use the HAProxy load balancer to redirect users from HTTP to HTTPS automatically in a few easy steps.

This blog post covers how to set up custom error pages in HAProxy in order to ensure consistent, branded messaging that supports any backend web stack.

Find out how you can detect and stop fake web crawlers by using Verify Crawler add-on which comes included with the HAProxy Enterprise license.

In the blog post, you will learn how to become FIPS compliant using Red Hat Enterprise Linux 8 and HAProxy Enterprise for TLS encryption.

Learn how to use the dynamic SSL certificate storage introduced in HAProxy 2.1 and expanded in HAProxy 2.2 in order to update SSL certificates dynamically.

In this blog post, you will learn how to use HAProxy's Deny, Tarpit, Silent Drop, Reject, and Shadowban response policies to stop threats and malicious users.

Learn how to configure TLS with the HAProxy Kubernetes Ingress Controller to provide secure communication to everyone accessing your Kubernetes services.

In this blog post, you will find out more about the HAProxy Process Manager, which allows you to start external programs that are hosted under HAProxy.

In this blog post, we show step-by-step, how to install the HAProxy Kubernetes Ingress Controller into your Kubernetes cluster using the popular Helm charts
Learn to use the HAProxy Kubernetes Ingress Controller to host multiple tenants in a cluster and configure namespaces, access controls, and resource quotas.

This blog post covers how you can use HAProxy and the FastCGI protocol to ensure fast, secure, and observable load balancing of your PHP-FPM applications.

Learn how the HAProxy Kubernetes Ingress Controller supports rolling updates and blue-green deployments for updating your Kubernetes applications.

In this blog post, you'll see examples of recent trends in the modern proxy industry and learn how HAProxy is being shaped to accommodate these changes.

Learn more about the HAProxy Cross-Origin Resource Sharing (CORS) Lua module, which streamlines adding CORS to your APIs.

Use rate limiting in HAProxy to stop clients from making too many requests and promote fair usage of your services.

Learn how to use the HAProxy Traffic Shadowing agent to enable traffic mirroring and stream production requests to a test environment.

HAProxy 2.0 introduced layer 7 retries, which provides resilience against unreachable nodes, network latency, slow servers, and HTTP errors.

This blog post shows you how to use the HAProxy Data Plane API to manage your load balancer configuration dynamically using HTTP commands.

This blog post shows how to quickly and easily enable SSL/TLS encryption for your applications by using high-performance SSL termination in HAProxy.

Learn to monitor, troubleshoot, and manage your load balancer effectively with our deep dive into the HAProxy status page.

This blog post shows how to use HAProxy IP Masking in order to protect the privacy of your users, helping you to stay compliant with laws like the GDPR.

In the blog post, you'll learn various ways to health check your servers so that your APIs maintain a high level of reliability. This includes...
![Using HAProxy as an API gateway, part 3 [health checks]](https://cdn.haproxy.com/img/containers/partner_integrations/image2-2-%281%29.png/5ef4ef148b968f89804293c3d44312e7/image2-2-%281%29.png)
In the blog post, you'll learn more about using HAProxy as an API gateway, leveraging it to secure your API endpoints using OAuth 2.
![Using HAProxy as an API Gateway, Part 2 [Authentication]](https://cdn.haproxy.com/img/containers/partner_integrations/image2-e1548174430466.png/3942e9fa498bb46e325ba72db6f9bd84/image2-e1548174430466.png)
Learn how to set up an example project that uses gRPC and Protocol Buffers to stream messages between a client and a server with HAProxy in between.

In a service mesh, requests are passed to proxies that relay messages from one service to another. See how HAProxy can be used in the Consul service mesh.
