We're excited to announce the release of HAProxy Enterprise 3.3, which brings significant advancements to the HAProxy Enterprise WAF and bot management capabilities.
The high-performance HAProxy Enterprise WAF (patented) now has a unified multi-engine module for simpler configuration of both the Intelligent WAF Engine and optional Core Rule Set (CRS) compatibility mode, which supports OWASP CRS v4. The HAProxy Enterprise Bot Management Module, powered by the advanced Threat Detection Engine, now offers even more robust enforcement options with an enhanced CAPTCHA module that closes the door on sophisticated bypass techniques. This release further solidifies HAProxy Enterprise as a leading Web Application and API Protection (WAAP) solution.
Alongside this release, we are also announcing HAProxy ALOHA 18.0, which delivers OWASP CRS v4 support to the HAProxy ALOHA virtual or hardware load balancer.
HAProxy Enterprise 3.3 is a foundational component of the HAProxy One application delivery platform, in which the data plane, control plane, and secure edge network work together seamlessly to deliver ultra-low-latency application delivery and sovereign edge security.
New to HAProxy Enterprise?
HAProxy Enterprise load balancer provides high-performance load balancing for TCP, UDP, QUIC, and HTTP-based applications, high availability, an API/AI gateway, Kubernetes application routing, SSL processing, DDoS protection, bot management, global rate limiting, and a next-generation WAF.
HAProxy Enterprise combines the performance, reliability, and flexibility of our open-source core (HAProxy — the most widely used software load balancer) with ultra-low-latency security layers and world-class support. HAProxy Enterprise benefits from full-lifecycle management, monitoring, and automation (provided by HAProxy Fusion), and next-generation security layers powered by threat intelligence from HAProxy Edge and enhanced by machine learning.
Together, this flexible data plane, scalable control plane, and secure edge network form HAProxy One: the world’s fastest application delivery and security platform that is the G2 category leader in Load Balancing, API Management, Container Networking, DDoS Protection, and Web Application Firewall (WAF).
To learn more, contact our sales team for a demonstration or request a free trial.
What's new in HAProxy Enterprise 3.3
|
Feature |
Benefit |
Impact |
|
Unified HAProxy Enterprise WAF module |
A single module now manages both the Intelligent WAF Engine and CRS compatibility mode, unifying configuration and simplifying management |
Faster deployment and reduced risk of misconfiguration, leading to lower TCO |
|
OWASP CRS v4 support |
Run CRS v3 and v4 simultaneously, applying each to different traffic segments with independently configurable paranoia levels |
Zero-risk, gradual migration to the latest ruleset without disrupting production applications |
|
LB-CAPTCHA token-based callback verification |
Time-sensitive tokens protect the CAPTCHA callback process itself from replay attacks and automated bypass scripts |
Sophisticated bots are stopped at the verification stage before they can access protected resources |
|
Multiple CAPTCHA support |
Deploy different CAPTCHA configurations for different resources within the same application |
Fine-grained bot protection across complex application architectures |
|
Custom HTML injection |
Inject dynamic, per-request values into CAPTCHA HTML responses based on attributes such as User-Agent |
Advanced anti-bypass customization for high-security deployments |
What's new in HAProxy ALOHA 18.0
|
Feature |
Benefit |
Impact |
|
OWASP CRS v4 support |
Run CRS v3 and v4 simultaneously, applying each to different traffic segments with independently configurable paranoia levels |
Zero-risk, gradual migration to the latest ruleset without disrupting production applications |
Ready to upgrade?
When you are ready to start the upgrade procedure, go to the upgrade instructions for HAProxy Enterprise or the installation instructions for HAProxy ALOHA.
Unified HAProxy Enterprise WAF module
Web applications and APIs are the primary attack surface for modern enterprises, facing a continuously evolving threat landscape that includes injection attacks, cross-site scripting, broken authentication, and more. A WAF is an essential layer of defense — one that must be accurate enough to block real threats, fast enough to avoid adding latency, and flexible enough to adapt without disrupting legitimate traffic. As architectures grow more complex, consistent WAF policy management across the entire environment becomes equally critical.
HAProxy Enterprise 3.3 introduces a unified multi-engine module for the HAProxy Enterprise WAF. This module consolidates both WAF engines — the unique and powerful Intelligent WAF Engine and the CRS compatibility mode — under a common configuration interface.
The HAProxy Enterprise WAF is patented and recognized for its exceptional balanced accuracy (98.48%), ultra-low latency, and 100% private and local processing. The unified module brings together the Intelligent WAF Engine, powered by threat intelligence from HAProxy Edge and enhanced by machine learning, and the CRS compatibility mode, both delivering unparalleled performance within a single, consistent configuration interface.
The practical benefit is a simpler administrative experience: less configuration overhead, fewer opportunities for misconfiguration, and faster time-to-deployment. For enterprise teams managing complex or large-scale fleets, this directly improves operational velocity and reduces total cost of ownership.
When managed through HAProxy Fusion's visual security policy builder – the Threat-Response Matrix – administrators can orchestrate unified WAF policies across multi-cloud deployments from a single pane of glass.
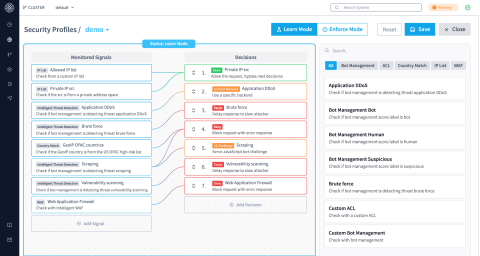
Visual orchestration of HAProxy Enterprise’s multi-layered security with the Threat-Response Matrix in HAProxy Fusion 2.0
OWASP CRS v4 support — upgrade at your own pace

The OWASP Core Rule Set (CRS) is the most widely deployed open-source WAF ruleset and is used to defend against the OWASP Top 10 and other common web attack categories. HAProxy Enterprise WAF uses the unique Intelligent WAF Engine by default, and provides an optional CRS compatibility mode for those who need it.
What sets HAProxy Enterprise WAF apart is the multi-engine architecture, where CRS works alongside the Intelligent WAF Engine to significantly boost accuracy and performance compared with standard CRS implementations. The result is a false positive rate of just 1.78% at paranoia level 2 (versus 28.36% for ModSecurity) and 15X lower latency.
HAProxy Enterprise 3.3 adds native support for CRS v4, which delivers improved detection accuracy, reduced false positives, and a more granular paranoia level system that gives security teams finer control over the trade-off between protection and permissiveness.
Crucially, HAProxy Enterprise 3.3 supports CRS v3 and v4 simultaneously — without requiring plugins — enabling teams to adopt the new ruleset entirely on their own terms.
With this release, administrators can:
load CRS v3 and v4 at the same time, applying each to different traffic segments;
set the paranoia level independently for each version, tailoring detection sensitivity to each application's risk profile; and
switch between versions or roll back at any time if needed.
This multi-version approach removes the forced hard-cutover that has historically made WAF ruleset migrations risky. Teams can test CRS v4 against a subset of traffic while keeping CRS v3 in place for production workloads, gradually building confidence before completing the transition.
The result is access to the better accuracy and performance that CRS v4 offers — without the application disruption that has made ruleset upgrades a stressful proposition.
OWASP CRS v4 support is also available in HAProxy ALOHA 18.0, bringing the same flexible multi-version migration path to teams running the ALOHA hardware or virtual appliance.
Enhanced bot protection with LB-CAPTCHA
Automated bot traffic is one of the most pervasive challenges facing application teams today. Bots range from harmless crawlers to sophisticated tools used for application-layer DDoS, brute force attacks, web scraping, and vulnerability scanning — and modern bots are increasingly designed to evade detection by mimicking human behavior. The business impact is substantial: fraudulent transactions, degraded performance, data theft, and damage to user trust.
Building on the advanced Bot Management solution, and the Threat Detection Engine introduced in version 3.2, HAProxy Enterprise 3.3 extends the LB-CAPTCHA module with several capabilities designed to stop more sophisticated bots.
Token-based CAPTCHA callback verification
The most significant enhancement is a new token-based verification mechanism that protects the CAPTCHA callback process itself. When a user completes a CAPTCHA challenge, HAProxy generates a time-sensitive token from request headers during the initial GET request. On the subsequent POST request, the token is verified. Because automated bots typically modify their headers between requests, they produce a mismatched token and are blocked immediately — before they can reach the verification server.
This protection is enabled by default, applying to all CAPTCHA deployments without additional configuration. For environments requiring stricter security, the new callback-token function allows administrators to customize token generation using advanced criteria such as full HTTP or SSL client fingerprints.
Multiple CAPTCHA support
HAProxy Enterprise 3.3 introduces support for multiple CAPTCHAs within the same application. Administrators can now apply different CAPTCHA providers or configurations to different resources — for example, one CAPTCHA for a login endpoint and another for a checkout flow — giving security teams finer-grained, per-resource control over bot protection.
Custom HTML injection
A new custom-html-file-lf option enables dynamic HTML injection in CAPTCHA responses. Administrators can inject changing values on a per-request basis, allowing the rendered output to vary based on attributes such as the User-Agent string. This capability is particularly valuable in high-security deployments where static CAPTCHA pages may be more susceptible to scripted analysis.
Building on the HAProxy One platform
HAProxy Enterprise 3.3 continues a consistent trajectory of security advancement within the HAProxy One platform. HAProxy Enterprise 2.9 introduced the next-generation HAProxy Enterprise WAF, with the Intelligent WAF Engine delivering industry-leading balanced accuracy of 98.48%. HAProxy Enterprise 3.2 introduced the Threat Detection Engine to the Bot Management Module, bringing SaaS-level behavioral detection to your own infrastructure — including air-gapped environments. HAProxy Fusion 2.0 provides the centralized security control plane to orchestrate WAF, bot management, and more across large-scale, multi-cloud deployments from a single intuitive interface.
Together, these releases establish HAProxy One as a top-tier WAAP platform that delivers the sophisticated protection of a cloud SaaS solution with the uncompromised control of a localized, sovereign data plane and control plane.
Breaking change: HAProxy Enterprise Data Plane API 3.3 updated crt_load endpoint structure
HAProxy Enterprise 3.3 releases alongside an updated version of the HAProxy Enterprise Data Plane API that includes a structural improvement to the crt_load endpoints. These endpoints are now correctly nested under their parent crt_store resource, aligning the API structure with the HAProxy configuration model, in which crt-load directives exist within a crt-store section.
The updated endpoint paths are as follows:
Operation | Updated Endpoint |
List |
|
Create |
|
Get |
|
Update |
|
Delete |
|
All crt_load operations now require the {crt_store} path parameter to identify the parent crt-store section. Clients using the previous endpoint paths should update their API calls to include the crt_store name in the path before upgrading to HAProxy Enterprise 3.3.
Deprecation notice: HAProxy Enterprise Data Plane API 3.3 endpoints
With the release of HAProxy Enterprise Data Plane API 3.3, two endpoint groups are being formally deprecated and scheduled for removal in v3.4.0. This notice is intended to give teams sufficient time to plan and complete their migrations.
/services/git endpoints — The Git-based configuration management endpoints are deprecated as of v3.3.0. Teams currently using these endpoints for configuration workflows should transition to alternative configuration management approaches ahead of the v3.4.0 release.
/services/aloha endpoints — The HAProxy ALOHA service management endpoints are also deprecated as of v3.3.0. Users relying on these endpoints should evaluate and adopt alternative service management workflows before upgrading to v3.4.0.
Both endpoint groups remain fully functional in v3.3.0, giving teams a stable migration window. They will be removed entirely in v3.4.0.
Endpoint Group | Status in v3.3.0 | Status in v3.4.0 |
| Deprecated (functional) | Removed |
| Deprecated (functional) | Removed |
Users who depend on either of these endpoint groups are encouraged to begin planning their migration now. If you have questions about suitable alternatives or need guidance on your migration path, please contact our support team.
Deprecation notice: HAProxy Enterprise 3.3 master-worker configuration keyword
The master-worker keyword in haproxy.cfg is deprecated as of HAProxy Enterprise 3.3 and will be removed in version 3.5. Users currently enabling master-worker mode via this configuration directive should migrate to the equivalent command-line flags before upgrading to 3.5.
Migration path: Replace master-worker in your configuration file with the -W flag (or -Ws for silent mode) passed directly to the HAProxy binary in your startup script.
Deprecated (haproxy.cfg) | Replacement (startup script) |
|
|
The master-worker keyword remains fully functional in 3.3, giving teams a stable migration window ahead of the 3.5 removal.
Upgrade to HAProxy Enterprise 3.3 or HAProxy ALOHA 18.0
When you are ready to upgrade, follow the links below.
Documentation | Release Notes | Install Instructions |
Try HAProxy Enterprise or HAProxy ALOHA with a free trial
The world’s leading platforms and cloud providers trust HAProxy Technologies to simplify, scale, and secure modern applications, APIs, and AI services in any environment. HAProxy Enterprise 3.3 and HAProxy ALOHA 18.0 continue our commitment to delivering industry-leading application delivery and security without compromise. Whether you're running HAProxy Enterprise as a software data plane or HAProxy ALOHA as a hardware or virtual appliance, these releases give you the tools to adopt the latest WAF standards and manage your security posture with greater simplicity — all within the HAProxy One platform.
To see for yourself, request a free trial:
Subscribe to our blog. Get the latest release updates, tutorials, and deep-dives from HAProxy experts.