
The EU's cybersecurity mandate is in effect. Here’s how HAProxy supports your regulatory requirements.
With NIS2 and DORA now in effect, EU organizations face a fundamental shift in how they approach security. Compliance is a standard built into every layer of your environment, from your hardware and OS to your software configuration.
HAProxy alone doesn't make an organization compliant, yet it serves as a critical technical component of a strong security strategy. By providing multi-layered security at the application layer, HAProxy Enterprise helps teams meet the technical expectations of these mandates as part of their broader security infrastructure.
This post is for informational purposes only and does not constitute legal advice. Organizations should consult legal and compliance professionals to ensure full compliance with NIS2 and DORA.
NIS2 vs DORA: what do they require?
The European Union introduced NIS2 and DORA with a clear mission: to protect the essential services that EU citizens rely on every day. From power grids and telecommunications to local governments and banking systems, these critical sectors are increasingly targeted by ransomware, DDoS attacks, and other sophisticated threats.
Both frameworks mandate that organizations raise their cybersecurity and operational resilience standards to ensure they remain secure, reliable, and operationally stable.
NIS2: strengthening cybersecurity across essential services
NIS2 (Network and Information Security Directive 2) builds upon the original NIS Directive, introducing stricter requirements and encompassing a broader range of sectors.
It mandates that organizations implement appropriate and proportionate technical, operational, and organizational measures to manage cybersecurity risks.
In practice, this means:
Conducting regular risk assessments to find and fix vulnerabilities.
Establishing transparent processes for incident detection and reporting within strict deadlines.
Ensuring business continuity and recovery capabilities.
Managing supply chain security and implementing safeguards such as encryption and access control.
Making executive management accountable for security decisions.
NIS2 applies to critical entities in industries such as energy, transport, healthcare, digital infrastructure, public administration, food production, and manufacturing.
DORA: what financial institutions must prove
While NIS2 casts a wide net, the Digital Operational Resilience Act (DORA) focuses specifically on financial institutions and their technology providers.
DORA requires a comprehensive framework for operational resilience, ensuring financial entities can withstand, respond to, and recover from all information and communication technology (ICT) related incidents. To comply, organizations must:
Establish a formal framework for managing information and communication technology risks.
Implement continuous monitoring and threat intelligence.
Conduct advanced digital operational resilience testing.
Maintain robust incident classification and reporting.
Oversee and audit critical third-party providers.
This regulation affects banks, insurers, investment firms, payment processors, crypto-asset providers, and the cloud or information and communication technology vendors that serve them.
What are the penalties under NIS2 and DORA?
Non-compliance penalties under NIS2 and DORA are intentionally severe to ensure high-level accountability.
The EU has established one of the most stringent accountability frameworks with the NIS2 and DORA regulations. Non-compliance with NIS2 can result in fines reaching up to €10 million or 2% of global turnover. Similarly, DORA imposes fines of up to 2%, with the potential for daily penalties for continuous non-compliance.
Summary of NIS2 and DORA requirements
NIS2 | DORA | |
Who it applies to | Essential and important entities in sectors such as energy, healthcare, transport, public administration, digital infrastructure, and manufacturing. | Financial institutions and ICT third-party providers, including banks, insurers, investment firms, and crypto-asset service providers. |
Management liability and sanctions | • Executives (CEOs, board members) can be personally liable for gross negligence. [1] • Possible temporary bans from management roles. • Public disclosure of violations. • Mandatory audits and compliance orders. | • Management must maintain operational resilience and enforce oversight of ICT vendors. • Authorities can publish penalty details, including the nature of the breach and responsible entities. |
Enforcement focus | Builds a culture of accountability from leadership downward, making cybersecurity a core business priority. | Promotes transparency and public trust by ensuring financial stability and visibility into regulatory actions. |
Bottom line | ||
Financial penalties | • Essential entities: up to €10 million or 2% of global turnover (whichever is higher). • Important entities: up to €7 million or 1.4% of global turnover.[1] | • Up to 2% of global annual turnover. • Daily penalties possible for ongoing non-compliance. [2] |
From legalese to technical reality: the implicit mandate for application security
The NIS2 Directive and DORA define high-level outcomes rather than specific toolsets: protect critical services, manage risk, detect and report incidents, and maintain evidence of your resilience. Because these goals inherently rely on the availability and integrity of your applications, strong Layer 7 controls become a vital component of your defense strategy.
In practice, a web application firewall is one of the most effective ways to implement visible, logging-rich security at the application layer. In the HAProxy Enterprise load balancer, the HAProxy Enterprise WAF sits alongside built-in application-layer DDoS protection and the HAProxy Enterprise Bot Management Module, allowing you to address exploits, floods, and automated abuse as a critical layer in your overall security infrastructure.
How HAProxy helps meet technical expectations
Building a resilient infrastructure requires a "defense-in-depth" approach that protects services thoroughly. Since many modern attacks target the application layer, organizations must consider how to mitigate these specific threats.
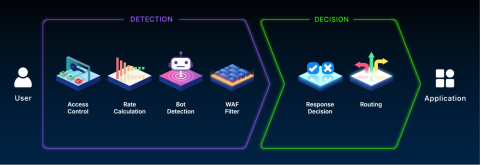
WAF protection solution. Application-layer protection including deep request inspection, policy enforcement, and detailed logs, supporting incident detection, reporting, and virtual patching. This functionality is critical for covering the full spectrum of application-layer risks.
Application-layer DDoS protection solutions. Global rate limiting, surge handling, connection management, adaptive challenges, and circuit breakers help maintain availability during floods and abusive traffic patterns.
Bot management solutions. Fast and flexible identification and categorization of bots, including unwanted crawlers and scripted attackers, so teams can block automated abuse (including brute force attacks, web scrapers, and vulnerability scanners) while preserving traffic from humans and verified crawlers.
What to consider for auditability
While the directives do not prescribe a specific product, and requirements vary by industry and nation, demonstrating operational resilience often requires evidence of robust technical controls. Capabilities that help demonstrate this resilience include:
WAF for exploit prevention and virtual patching.
Layer 7 DDoS protections for rate control and graceful degradation.
Bot management for detecting, classifying, and labeling a broad spectrum of complex, high-impact threats.
HAProxy Fusion centralizes HAProxy logs and telemetry, aggregating real-time metrics and security logs for formal reporting and audit trails.
These capabilities provide practical coverage of application-layer risks, offering the data and visibility teams need to support their compliance assessments.
HAProxy Enterprise combines these capabilities within a single layer in the traffic path, delivering high performance and low complexity.
The compliance crossroads
Organizations now face a choice between two paths.
The traditional way: complexity through bolt-on solutions
Some teams opt to deploy a separate, standalone WAF appliance or cloud service. This can introduce new challenges, such as:
Added latency and network hops that slow down applications.
Integration conflicts between different vendors and architectures.
Higher total cost of ownership due to extra licenses, training, and monitoring tools.
Another potential point of failure in the data path.
The HAProxy way: simplicity through unification
Instead of stacking tools, a smarter path is to build security into the platform you already trust. That’s where HAProxy Enterprise load balancer comes in.
HAProxy Enterprise: a key component of your compliance strategy
HAProxy Enterprise provides high-performance load balancing for TCP, UDP, QUIC, and HTTP-based applications, high availability, an API/AI gateway, Kubernetes application routing, SSL processing, DDoS protection, bot management, global rate limiting, and a next-generation WAF.
HAProxy Enterprise is built on the highly regarded open-source HAProxy, the most widely used software load balancer, ensuring exceptional performance, reliability, and flexibility. It enhances this core with ultra-low-latency security features and includes premier support.
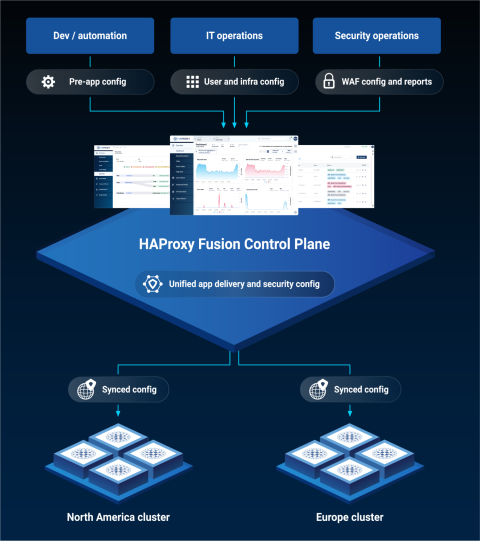
HAProxy Enterprise benefits from full-lifecycle management, monitoring, and automation (provided by HAProxy Fusion), and next-generation security layers powered by threat intelligence from HAProxy Edge and enhanced by machine learning.
Resilience without compromise
Security often comes with trade-offs, but not here. HAProxy Enterprise integrates advanced defenses directly into the HAProxy instance you already have in the traffic path, helping to support the technical side of your business continuity plans.
Zero additional latency and low resource use: The WAF operates natively inside the load balancer, scanning and blocking malicious traffic inline, without increasing latency or CPU use.
Seamless upgrade path: Upgrading from HAProxy Community to HAProxy Enterprise requires no new hardware or network redesigns; your existing HAProxy configurations and automation continue to work seamlessly.
Consistent cross-environment protection: Deploy on-premises, in containers, or across multiple clouds with the same security posture everywhere.
The result is security at the speed of your business, providing robust technical controls that are invisible to users and simple for your teams to manage.
Roblox uses HAProxy Enterprise WAF to protect over 100 million daily users without impacting latency or player experience. Infobip deploys it across 62 global data centers, handling 80,000 transactions per second while meeting strict contractual latency requirements.
The smartest move is an upgrade
Both NIS2 and DORA demand that organizations prove their resilience. That means having the proper controls, visibility, encryption, risk management, and continuity built into the heart of your infrastructure.
With HAProxy Enterprise, you don’t need extra tools or added complexity. High availability, built right into our name, ensures your infrastructure performs reliably under heavy loads or security events. Strengthen your security posture through the same platform you trust for traffic delivery, now enhanced with enterprise-grade protection and observability to support your compliance efforts.
Ready to see it in action?
Have questions about how HAProxy fits into your compliance strategy?
|
Note on Compliance: HAProxy Enterprise provides robust security and observability to help organizations manage application-layer risks. However, achieving compliance with regulations such as NIS2 or DORA depends on a customer’s overall security infrastructure, operating environment, and the management of their broader risk program. The examples provided in this article are for illustrative purposes only and do not constitute a legal guarantee or a promise of compliance.
[2] Final text of the Digital Operational Resilience Act (DORA)
Subscribe to our blog. Get the latest release updates, tutorials, and deep-dives from HAProxy experts.



