Getting started
Overview of HAProxy Enterprise
Today, many web applications experience high traffic demands, and traffic spikes can lead to server overloads and a deteriorating user experience.
The HAProxy Enterprise software load balancer spreads traffic across a pool of healthy servers, allowing you to scale out your capacity for handling concurrent requests. You can then easily answer the demand, while also improving performance and availability.
You can seamlessly integrate HAProxy Enterprise with your existing infrastructure, such as:
- At the edge of a network to replace traditional hardware load balancers.
- In the cloud to replace expensive virtual load balancers.
- Inside a container network as a sidecar proxy.
When you deploy HAProxy Enterprise, HAProxy Technologies, LLC. doesn’t store or process any data of your customers related to any traffic flows through your load balancers.
The job of a load balancer Jump to heading
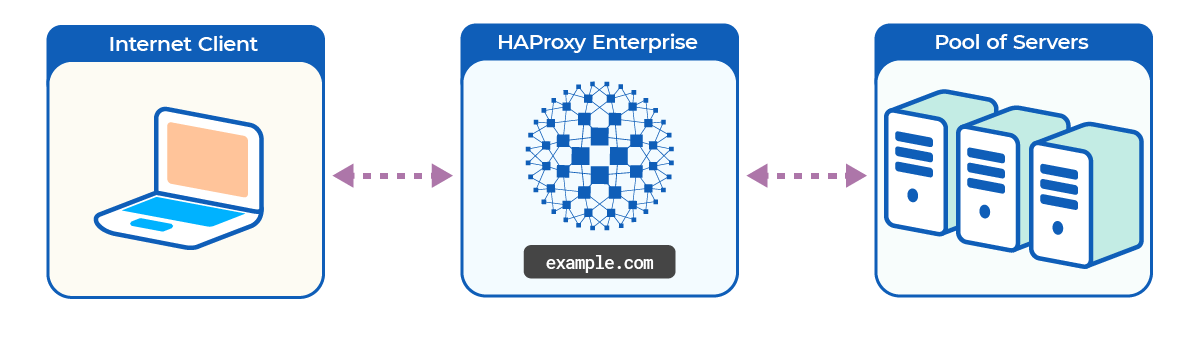
A load balancer sits in front of your web servers and receives requests directly from clients before relaying them to your servers. In this way, the load balancer can distribute requests evenly, allowing the work to be shared. This workload sharing prevents any backend server from becoming overworked, so your servers operate more efficiently. A load balancer differs from a web or application server in that it doesn’t host your web application directly. Instead, its job is to spread the work across your cluster of servers.
Because all requests pass through the load balancer on their way to a server, the load balancer becomes the ideal place to redirect clients, inspect for malicious behavior, and generate traffic statistics, among other duties. HAProxy Enterprise provides security and management features in addition to load-balancing. You can use it to load balance any TCP/IP service, including databases, message queues, mail servers, and IoT devices.
HAProxy Enterprise features Jump to heading
HAProxy Enterprise offers:
- Comprehensive load balancing algorithms
- Customizable routing logic
- Session persistence
- Device detection
- Geolocation
- Support for load balancer clustering and high availability
- Bot management
- A Web Application Firewall
HAProxy Enterprise integrates seamlessly with your existing infrastructure and can run in the cloud, on-premises virtual machines, or as a Docker container. It routes traffic to any number of server pools comprising physical servers, VMs, Kubernetes pods, and containers.
Download the HAProxy Enterprise datasheet for more details.